BIECO
The general objective of BIECO is to develop a framework that enables measurable, risk-based trust while developing, deploying and operating complex interconnected ICT systems.
Objectives
We aim to achieve this by handling the reliability and trust aspects of ecosystem participants (ICT systems, ICT system components and actors) within the supply chain.
The following shows the specific SMART (Specific, Measurable, Achievable, Realistic, Time-bound) objectives of the project, taking into account the challenges of this kind of complex ecosystems.
Framework
Providing a framework that allows reinforcing trust in ICT supply chains (WP2).
Vulnerability assessment
Performing advanced vulnerability assessment over ICT supply chains (WP3).
Achieving resilience
Achieving resilience in ecosystems formed by unreliable components (WP4).
Extending auditing
Extending auditing process to evaluate interconnected ICT systems (WP5).
Advanced risk analysis
Provide advanced risk analysis and mitigation strategies that support a view of the complete ICT supply chain (WP6).
Security assurance
Perform evidence-based security assurance and a harmonized certification for ICT systems (WP7).
Industrial validation
Industrial validation of BIECO’s framework within IoT ecosystems (WP8).
Exploitable Results
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
About BIECO
The rationale behind BIECO’s concept is to deliver a framework for improving trust and security within ICT supply chains. These are complex ecosystems comprising several heterogeneous technologies, processes, actors (e.g., end-users, software or hardware providers and organizations) and resources, all of which generate or exchange data forming extremely complex information management systems.
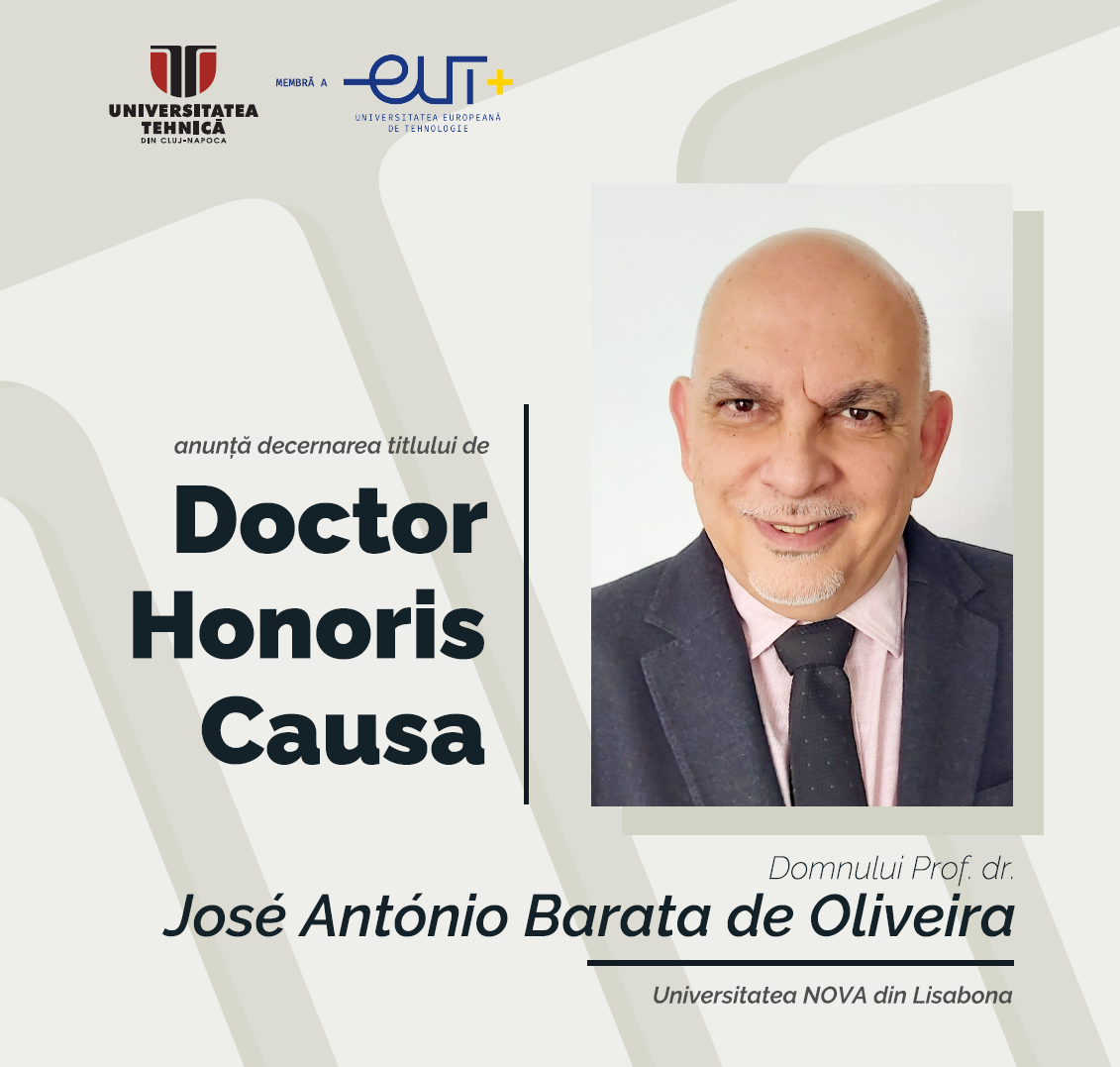
The BIECO team is proud to announce
NEWS
Monitoring Tool
Monitoring Tool Coordinated byCNRThe monitoring tool is an infrastructure in charge of setting up and managing a monitoring component. It is based on event messages and enables the collection of complex events.DescriptionDescribe the innovation content of the result:...
Security Testing Tool
Security Testing Tool Coordinated byCNRGdpR-based cOmbinatOrial Testing (GROOT) is a general combinatorial strategy for testing systems managing GDPR’s concepts (e.g., Data Subject, Personal Data or Controller).DescriptionDescribe the innovation content of the result:...
Domain Specific Language
Domain Specific LanguageCoordinated byIESEThe domain specific language enables specification of digital twin behaviour in a manner that can enable a predicted evaluation of its trustworthy behaviour in a simulated environmentDescriptionDescribe the innovation content...
Fail-operation clock synchronization methodology
Fail-operation clock synchronization methodology Coordinated byTTTechSynchronization loss can occur due to many reasons, either because of a device or link failure or due to a targeted attack on the reference node, which supplies the corrected time to the network’s...
Time sensitive network simulation
Time sensitive network simulation Coordinated byTTTechSimulate the real time communication for the distributed based on the Time sensitive network simulation. Additionally, simulate the fail-operation clock synchronization methodology. This simulation will validate...
Remote updating- upgrading of vehicle firmware
Remote updating- upgrading of vehicle firmwareCoordinated byI-FEVSSecuring remote and in-vehicle communications against cyber-attacks, possibly performed with quantum computers in the near future, is a major goal in the automotive sector. For such a purpose I-FEV...












