WP6 – Risk Analysis and Mitigation Strategies
Coordinated by
RES (M01-M16)
Objective
This work package researches and develops a methodology for continuous risk assessment process on the ICT supply chain, such that the system is continuously analyzed for potential weaknesses, and corresponding mitigation strategies can be enacted using BIECO solutions.
This WP has the following concrete objectives:
- To identify in an automated fashion main threats, including those that could also derive in a physical hazard in a cyber-physical system.
- To compute the severity of the consequences of threats and hazards.
- To make the link between systems’ internal security causes and their possible safety hazards explicit, e.g. in failure logic models such as Component Fault Trees.
- To define mitigation strategies.
- Out of both design time risk assessment models and mitigation strategies, runtime risk management models shall be synthesized systematically that are suitable to support runtime resilience mechanisms defined in WP4.
- Design and develop security, privacy and accountability measures for all the entities involved in the supply chain.
Envisioned mitigations range from process-based to architecture-based as well as related to the introduction of new patches and error detectors. The WP will ultimately produce a methodology and supporting tools for the systematic and automated i) analysis of risks, and ii) identification of mitigations that shall be equipped in the BIECO framework.
Deliverables
- D6.1 Blockly4SoS model and simulator WP6 (7 – RESILTECH) Report Public M10
- D6.2 Blockly4SoS user guide WP6 (7 – RESILTECH) Report Public M12
- D6.3 Risk Assessment and additional requirements WP6 (10 – 7BULLS) Report Public M24
- D6.4 Mitigations identification and their design WP6 (2 – Fraunhofer) Report Public M16
Outcomes
A comparative study of the most important methods for forecasting the ICT systems vulnerabilities
Authors: Ovidiu Cosma, Mara Hajdu-Macelaru, Petrica Pop-Sitar, Cosmin Sabo, Ioana Zelina
Comparison of Safety and Security analysis techniques
Authors: Emilia Cioroaica, Smruti Ranjan Kar, and Ioannis Sorokos
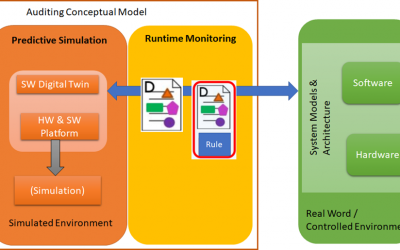
BIECO Runtime Auditing Framework
Authors: Antonello Calabro, Emilia Cioroaica, Said Daoudagh, and Eda Marchetti
Goals within Trust-based Digital Ecosystems
Authors: Emilia Cioroaica, Akanksha Purohit, Barbora Buhnova, and Daniel Schneider
Bridging Trust in Runtime Open Evaluation Scenarios
Authors: Emilia Cioroaica, Barbora Buhnova, Eda Marchetti, Daniel Schneider, and Thomas Kuhn
BIECO M12 Progress Meeting
BIECO M12 Progress Meeting Agenda 7-8th September 2021, 09:00- 15:00 CET Location: Teams – General Meeting Objectives: Check the progress statusAlign the work in all WP’sAlign the view of the participants with the vision of the project Attendees: Representatives of...